Suzie
Legit VIP
Insider Tricks
By Susan Bradley
Potentially dangerous scam e-mails might be landing in your inbox, masquerading as legitimate mail.
Fortunately, there are tools that can help you determine the source of suspect messages and possibly identify who’s sending them.
Malicious e-mails are getting harder to detect
Recently, some PC users have received suspicious e-mails containing attached Word documents. Hidden within the Word docs was a zero-day bug that automatically installed itself when the documents were opened. A Nov. 1 Symantec blog gives a detailed explanation of how it works.
The Symantec blog notes that the Word files were cleverly designed to look like legitimate documents recipients might expect to receive. This goes well beyond the old Nigerian financial-aid ploys. Computer users have even received forged Facebook e-mails that appear completely authentic. But click the familiar yellow “See the comment thread” box, and you could be infected. The U.S. Federal Bureau of Investigation’s New E-Scams & Warnings page notes other types of e-mail scams, such as responses to online job postings and lottery notifications. And then there are those notorious PDF attachments.
I’m seeing a growing number of scam e-mails on both my business and personal accounts. My spam filters catch most of these, but I maintain one unfiltered e-mail account to keep an eye on the latest spoofs. For example, now that businesses are moving to electronic payroll and income-tax filings, I’m receiving malicious e-mail disguised as official payment messages. I’ve also seen PayPal-transaction spoofs and other online payment alerts. I’ve even come across bogus notices from the FBI and the U.S. Internal Revenue Service, two agencies that can strike the fear-of-compliance in recipients. (The IRS still does not send e-mails to taxpayers. It gives you the bad — or occasionally good — news by printed correspondence.)
Dissecting mail headers can provide useful info
So how do you pick out these impostors lurking in your inbox? As I’ve said many times, the first rule is to be suspicious of 1) any unexpected mail with attachments or 2) mail from someone (or some company) you’re unfamiliar with. Any message that asks for personal information is immediately suspect.
The second step is to pick apart the message’s header. (As you probably already know, spoofing an e-mail’s From address is easy.) But looking more deeply at the header can give you a heads-up that something is amiss.
The message-header file contains a history of how messages are handed off from one mail server to the next. Tracking e-mail headers isn’t new: numerous white papers on the Internet, such as Marwan Al-Zarouni’s “Tracing e-mail headers” (PDF document), detail how it’s done.
Outlook — especially Outlook 2010 — doesn’t make dissecting message headers easy. An e-mail’s header information is hidden under File/Info/Properties. Look for the Internet Headers box at the bottom of the properties window.
Fortunately, there’s an easy-to-use tool — PocketKnife Peek (info/download) — that lets you peek into Outlook’s header file immediately. Once Peek is installed, simply right-click a message in Outlook’s Inbox and select Peek from the options list — a message-details window immediately pops up. Select the Internet Header tab. (See Figure 1.)

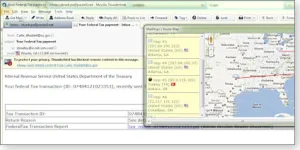
Figure 1. PocketKnife Peek lets you call up e-mail header information instantly.
What you’ll see is a raw, possibly confusing mash-up of text. But never fear, there are Web resources to help you decipher it. For example, copy everything in the Internet Header box and go to the iptrackeronline.com website (home page). Once there, click the Email Header Analysis button and paste the header information into the Paste email header here box. You get a nicely organized report of where the e-mail came from. (See Figure 2.)

Figure 2. Use iptrackeronline.com’s Email Header Analysis tool for an easy-to-read report of header information.
For example, the header information shown in Figures 1 and 2 was taken from an e-mail purportedly warning us that our online payroll wasn’t processed properly (shown in Figure 3.) The e-mail had the client’s correct name and the company’s address. Its “transaction was not processed” warning focuses the recipient’s attention on the possible problem — not the e-mail’s source.

Figure 3. This bogus e-mail looks like the real thing.
However, the header information shows that the e-mail was sent from Bogot
By Susan Bradley
Potentially dangerous scam e-mails might be landing in your inbox, masquerading as legitimate mail.
Fortunately, there are tools that can help you determine the source of suspect messages and possibly identify who’s sending them.
Malicious e-mails are getting harder to detect
Recently, some PC users have received suspicious e-mails containing attached Word documents. Hidden within the Word docs was a zero-day bug that automatically installed itself when the documents were opened. A Nov. 1 Symantec blog gives a detailed explanation of how it works.
The Symantec blog notes that the Word files were cleverly designed to look like legitimate documents recipients might expect to receive. This goes well beyond the old Nigerian financial-aid ploys. Computer users have even received forged Facebook e-mails that appear completely authentic. But click the familiar yellow “See the comment thread” box, and you could be infected. The U.S. Federal Bureau of Investigation’s New E-Scams & Warnings page notes other types of e-mail scams, such as responses to online job postings and lottery notifications. And then there are those notorious PDF attachments.
I’m seeing a growing number of scam e-mails on both my business and personal accounts. My spam filters catch most of these, but I maintain one unfiltered e-mail account to keep an eye on the latest spoofs. For example, now that businesses are moving to electronic payroll and income-tax filings, I’m receiving malicious e-mail disguised as official payment messages. I’ve also seen PayPal-transaction spoofs and other online payment alerts. I’ve even come across bogus notices from the FBI and the U.S. Internal Revenue Service, two agencies that can strike the fear-of-compliance in recipients. (The IRS still does not send e-mails to taxpayers. It gives you the bad — or occasionally good — news by printed correspondence.)
Dissecting mail headers can provide useful info
So how do you pick out these impostors lurking in your inbox? As I’ve said many times, the first rule is to be suspicious of 1) any unexpected mail with attachments or 2) mail from someone (or some company) you’re unfamiliar with. Any message that asks for personal information is immediately suspect.
The second step is to pick apart the message’s header. (As you probably already know, spoofing an e-mail’s From address is easy.) But looking more deeply at the header can give you a heads-up that something is amiss.
The message-header file contains a history of how messages are handed off from one mail server to the next. Tracking e-mail headers isn’t new: numerous white papers on the Internet, such as Marwan Al-Zarouni’s “Tracing e-mail headers” (PDF document), detail how it’s done.
Outlook — especially Outlook 2010 — doesn’t make dissecting message headers easy. An e-mail’s header information is hidden under File/Info/Properties. Look for the Internet Headers box at the bottom of the properties window.
Fortunately, there’s an easy-to-use tool — PocketKnife Peek (info/download) — that lets you peek into Outlook’s header file immediately. Once Peek is installed, simply right-click a message in Outlook’s Inbox and select Peek from the options list — a message-details window immediately pops up. Select the Internet Header tab. (See Figure 1.)

Figure 1. PocketKnife Peek lets you call up e-mail header information instantly.
What you’ll see is a raw, possibly confusing mash-up of text. But never fear, there are Web resources to help you decipher it. For example, copy everything in the Internet Header box and go to the iptrackeronline.com website (home page). Once there, click the Email Header Analysis button and paste the header information into the Paste email header here box. You get a nicely organized report of where the e-mail came from. (See Figure 2.)

Figure 2. Use iptrackeronline.com’s Email Header Analysis tool for an easy-to-read report of header information.
For example, the header information shown in Figures 1 and 2 was taken from an e-mail purportedly warning us that our online payroll wasn’t processed properly (shown in Figure 3.) The e-mail had the client’s correct name and the company’s address. Its “transaction was not processed” warning focuses the recipient’s attention on the possible problem — not the e-mail’s source.

Figure 3. This bogus e-mail looks like the real thing.
However, the header information shows that the e-mail was sent from Bogot
Attachments
Last edited: